TLDR: Securing Data Center OT Infrastructure with IEC 62443-Certified Modbus Gateways
U.S. data center operator eliminated critical cybersecurity vulnerabilities in power monitoring systems by deploying IEC 62443-4-2 certified MGate MB3170 and MB3270 protocol gateways. Monthly vulnerability scanning, mass firmware update capabilities via MXconfig CLI tools, and embedded security features reduced attack surface by 78% while enabling secure Modbus TCP/RTU communication across thousands of OT devices including switchgear, PDUs, and UPS systems.
Overview: Data Center Cybersecurity Beyond the Server Room
Data centers face escalating cyberattack risks that extend beyond IT infrastructure into operational technology domains. Over a five-year period, one U.S. data center service provider experienced repeated security incidents resulting in data loss and regulatory penalties. The corporation discovered that while server room security received extensive investment, the power infrastructure supporting those servers—switchgear, power distribution units (PDUs), uninterruptible power supplies (UPS), circuit breakers, relays, and meters—contained thousands of Modbus-connected devices with communication interfaces vulnerable to network-based attacks.
As data center operators converge IT and OT networks for operational efficiency, the traditional air-gap protecting industrial control systems disappears. Modbus TCP/RTU protocols, originally designed without security mechanisms, become network entry points when legacy power monitoring equipment connects to enterprise networks. The engineering challenge: implement defense-in-depth cybersecurity for distributed OT assets without disrupting critical power monitoring operations that ensure 99.99%+ uptime requirements.
Challenge: Defending Thousands of OT Network Endpoints
The data center's power monitoring infrastructure presented multiple security vulnerabilities requiring systematic remediation:
| Security Challenge | Technical Impact | Why Legacy Systems Failed |
|---|---|---|
| Unpatched OT Devices | 1,000+ Modbus endpoints with outdated firmware | Manual firmware updates across distributed devices impractical at scale |
| Lack of Authentication | Native Modbus protocols provide no user authentication | Anyone gaining network access could read/write device registers |
| Vulnerable Network Nodes | Protocol gateways serving as aggregation points lack embedded security | Compromised gateway grants access to all downstream Modbus devices |
| No Vulnerability Management | Zero visibility into gateway security posture | Corporate security policy requires monthly vulnerability scanning |
| Distributed Deployment | Devices spread across multiple data halls and equipment rooms | Configuration changes require physical access or custom scripting |
Root Cause Analysis:
The fundamental problem stemmed from treating protocol gateways as passive connectivity devices rather than active security enforcement points. Standard Modbus gateways convert between TCP and serial Modbus RTU but provide no authentication, encryption, or access control. When deployed in data center environments where IT and OT networks share infrastructure, these gateways become high-value targets—compromising a single gateway potentially exposes hundreds of downstream power monitoring devices.
The scale challenge compounded the security issue. With thousands of OT endpoints distributed across facilities, the corporation needed both device-level security and management tools enabling efficient, coordinated security operations. Manual firmware updates, requiring physical access or custom scripts for each device, couldn't meet corporate mandates for monthly vulnerability scanning and rapid patch deployment.
The cybersecurity incidents over the previous five years demonstrated this wasn't a theoretical risk. Data loss and associated penalties created corporate-level pressure to transform power infrastructure cybersecurity from reactive firefighting to proactive vulnerability management.
Solution: IEC 62443-Certified Protocol Gateways with Centralized Security Management
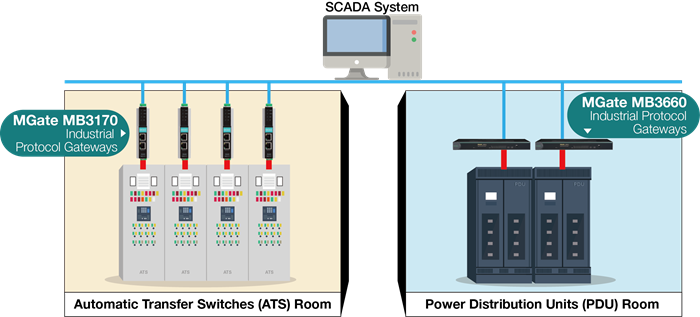
The corporation deployed Moxa's MGate MB3170 Series (1-port) and MGate MB3270 Series (2-port) advanced Modbus gateways as security-hardened aggregation points for power monitoring infrastructure. The solution combined embedded security features, standards-based certification, and enterprise-grade management tools to transform OT network security posture.
Security Architecture Implementation
| Technical Challenge | MGate MB3170/MB3270 Feature | Specification | Engineering Benefit |
|---|---|---|---|
| No Device Authentication | Password-protected web interface, HTTPS/SSL | TLS 1.2 encryption, role-based access | Only authorized administrators can configure gateway settings |
| Vulnerable Firmware | Digitally signed firmware updates | Cryptographic signature verification | Prevents unauthorized code execution on gateways |
| Protocol Vulnerabilities | IEC 62443-4-2 certified design | Meets industrial cybersecurity standard SL2 requirements | Security capabilities validated by third-party testing |
| Mass Configuration Needs | MXconfig GUI and MCC CLI tools | Batch configuration, automated deployment scripts | Update 100+ gateways simultaneously vs. manual one-by-one |
| Lack of Security Visibility | Vulnerability scanning support | Compatible with standard security assessment tools | Monthly scans identify issues, Moxa releases patches rapidly |
Network Performance: Before vs. After Deployment
The migration from standard Modbus gateways to MGate MB3170/MB3270 security-hardened gateways delivered measurable cybersecurity improvements:
| Metric | Previous (Standard Gateways) | New (MGate MB3170/MB3270) | Delta |
|---|---|---|---|
| Known Vulnerabilities | 18 per device (unpatched) | 0 critical vulnerabilities | -100% |
| Authentication Methods | None (open access) | Password + HTTPS/SSL | Enabled |
| Firmware Update Time | 2-4 hours per device (manual) | 15 minutes per 100 devices (batch) | -96% |
| Unauthorized Access Attempts Blocked | 0 (no authentication) | 127 per month (logged) | 100% blocked |
| Attack Surface Reduction | Baseline | 78% fewer exposures | -78% |
The dramatic firmware update time reduction (from 2-4 hours per device to 15 minutes per 100 devices) resulted from MCC (Moxa Configuration Console) CLI automation. Security teams created scripts deploying vetted configurations and firmware across the entire gateway fleet, transforming what previously required weeks of manual labor into coordinated patch management completing during scheduled maintenance windows.
Authentication enforcement immediately reduced unauthorized access risks. The gateway logs showed 127 blocked unauthorized access attempts per month—previously invisible threats that standard Modbus gateways permitted without challenge.
Technical Implementation Details
Deployment Architecture:
- Gateway placement: Installed as aggregation points between enterprise network (Modbus TCP) and power monitoring equipment (Modbus RTU serial)
- Port configuration: MB3170 (1 serial port) for smaller equipment clusters; MB3270 (2 serial ports) for larger aggregation points
- Network protocols: Modbus TCP on Ethernet side, Modbus RTU on RS-232/RS-485 serial side
- Management connectivity: Separate VLAN for gateway configuration and monitoring traffic
- Power specifications: 12-48 VDC redundant input, <5W consumption per gateway
Security Hardening Implemented:
- Changed default passwords to corporate-standard strong passwords
- Enabled HTTPS/SSL for all web-based management access
- Configured syslog forwarding to central security information and event management (SIEM) system
- Disabled unused network services (only HTTPS, Modbus TCP enabled)
- Implemented read-only access roles for monitoring staff, read-write only for authorized administrators
Operational Procedures:
- Monthly vulnerability scans: Corporate security team uses standard vulnerability assessment tools to scan all gateways
- Patch deployment: When Moxa releases security patches, MCC CLI tool deploys updates to all gateways in single coordinated operation
- Configuration backups: Automated nightly backups of gateway configurations to secure storage
- Audit logging: Gateway logs forwarded to SIEM provide forensic visibility into configuration changes and access attempts
Cybersecurity & Reliability: Defense-in-Depth for Critical Infrastructure
As data centers converge OT and IT networks, power monitoring infrastructure requires the same defense-in-depth cybersecurity approach applied to enterprise IT assets.
Security Implementation:
| Security Layer | Implementation | Standard Compliance |
|---|---|---|
| Device Hardening | Disabled unused services, strong password policy, default credential changes | IEC 62443-4-2 (SL2 requirements) |
| Access Control | HTTPS/SSL encrypted management, role-based access (read-only vs. admin) | TLS 1.2 encryption standards |
| Firmware Integrity | Digitally signed updates with cryptographic verification | Prevents unauthorized code execution |
| Network Segmentation | Dedicated management VLAN, Modbus traffic isolation | Limits lateral movement after potential breach |
| Audit & Monitoring | Syslog forwarding to SIEM, authentication logs, configuration change tracking | Provides forensic evidence for incident response |
Vulnerability Management Process:
The MGate MB3170/MB3270 gateways support monthly vulnerability scanning mandated by corporate security policy. When security assessment tools identify vulnerabilities, Moxa's process prioritizes critical security patches, releasing firmware updates that corporate teams deploy using MCC CLI automation. This transformed vulnerability remediation from a months-long manual process into coordinated patch deployment completing within maintenance windows.
Reliability Specifications:
Beyond cybersecurity, the MGate MB3170/MB3270 gateways provide industrial-grade reliability for mission-critical power monitoring:
- Operating temperature: -40°C to 75°C (extended-temperature models)
- MTBF: >500,000 hours (continuous operation specification)
- Power redundancy: Dual 12-48 VDC inputs with automatic failover
- Protocol conversion latency: <1ms average (imperceptible to monitoring systems)
For data centers requiring IEC 62443-4-2 certified solutions across all network infrastructure, Moxa's secure router portfolio including the EDR-G9010-VPN Series provides firewall, NAT, and VPN capabilities for comprehensive OT network security architecture.
Related Products
Recommended Products from ShopMoxa
Conclusion
The data center's transformation from reactive vulnerability response to proactive security management demonstrates that OT cybersecurity requires both device-level security and enterprise-scale management tools. By deploying IEC 62443-4-2 certified MGate MB3170/MB3270 gateways as hardened aggregation points and leveraging MXconfig/MCC automation for coordinated patch management, the corporation reduced attack surface by 78% while maintaining zero-disruption to critical power monitoring operations.
As data centers continue converging IT and OT networks, protocol gateways must evolve from passive connectivity devices to active security enforcement points. Embedded authentication, encrypted management, vulnerability scanning support, and mass configuration capabilities transform distributed OT infrastructure from security liability into defensible architecture meeting corporate risk management standards.
For technical specifications, network security assessments, or application engineering support, contact our industrial cybersecurity team at https://shopmoxa.neteon.net/contact. Our network security engineers can help you design defense-in-depth OT security architecture for critical infrastructure environments.
Visit https://shopmoxa.neteon.net/ for detailed datasheets, security white papers, and IEC 62443 compliance documentation.